CVE Automation Solution
A plugin is provided to automate the CVE solution end-to-end, minimizing manual effort while ensuring timely protection against the latest known vulnerabilities. The plugin automatically updates the existing CVEs and detects new ones, then updates the existing NIST versions and hardware information. In addition, it updates the associated automation resources, allowing users to monitor these vulnerabilities on an ongoing basis.
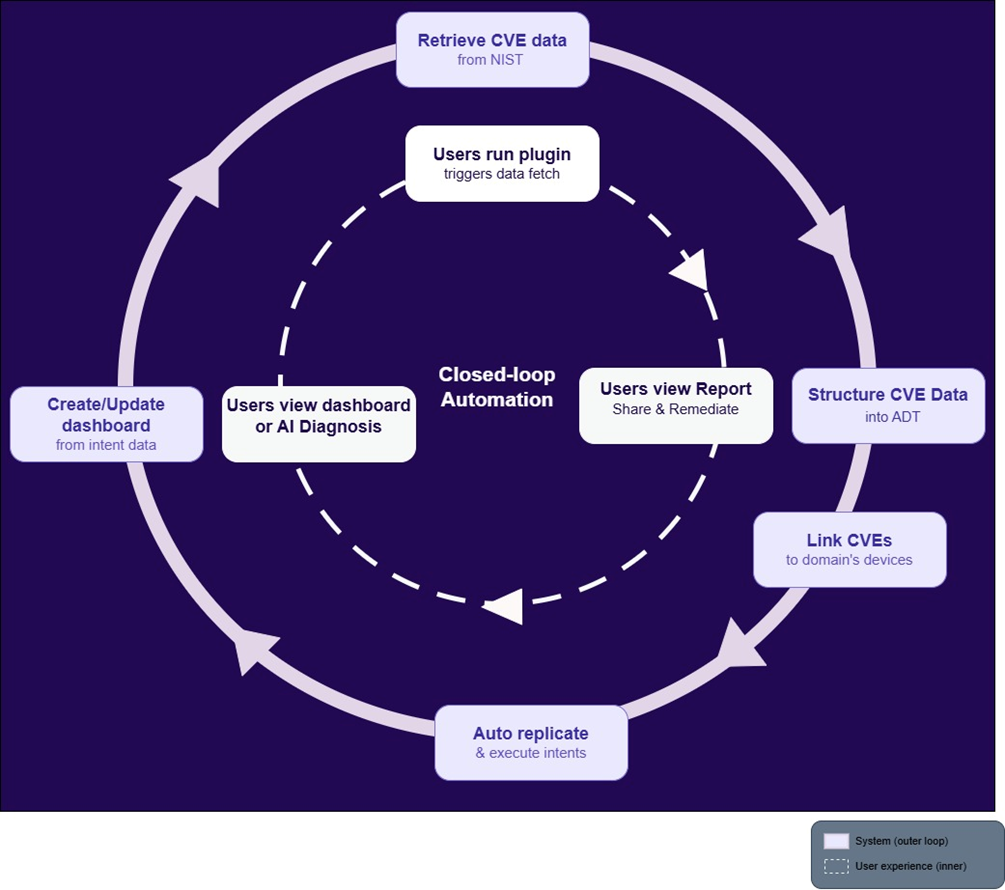
- Retrieves the latest published CVEs from NIST based on time range, severity, and/or specific CVE IDs.
- Structures CVE data into ADT tables as a reusable reference dataset.
- Links CVEs to your domain’s devices using vendor, OS and version data.
- Builds and executes intents to check and evaluate device exposure.
- Creates dashboards/reports so users can quickly see exposure. The CVE automation resources include network intents, automation data tables, and dashboards.
-
(Next execution cycle) The plugin continuously updates CVE data, scans the eligible devices, and presents the results. (The system repeats 1-5)

Note: The data from NIST may not always be accurate. In such cases, users can manually input the correct or updated information based on details from the vendor’s website, without having to wait for the next NetBrain patch release.
Supported vendors include Cisco, Arista, Juniper, Fortinet, Aruba, Kubernetes, Palo Alto, Check Point, VMware, and others. Please refer to the CVE Support List for the whole list. Once the plugin runs, only CVEs related to vendors present in the domain are used for automation and displayed on the dashboard.

|
Note: Before using this solution, uninstall any previously installed CVE-related packages. Note: If the user does not have a PA License, they may encounter issues when performing batch CVE checks under certain conditions. |